
Smart Cockpit
Protection
Securely Innovate AI-Powered Cockpits by Avoiding
Sensitive Data Leaks and Addressing Security Risks
AI-Powered Cockpit Risks: Battling Sensitive Data Leaks
In the first half of 2023 alone, the automotive industry lost over US$9.5 billion to data leaks and personally identifiable information (PII) exposure.* As the landscape of software-defined vehicles (SDVs) evolves, safeguarding user data becomes paramount. Our dynamic approach surpasses outdated static methods, adapting to real-world complexities and an expanding attack surface. VicOne's Smart Cockpit Protection leads the way with comprehensive protection against malicious AI apps, risky apps, phishing attacks, and privacy breaches — empowering OEMs, suppliers, insurance companies, and marketplace app providers to innovate confidently in the AI cockpit era.
*Source: VicOne Automotive Cyberthreat Landscape Report 2023
Securely Innovate in the AI Cockpit Era With Accurate, Scalable, and Thorough Protection
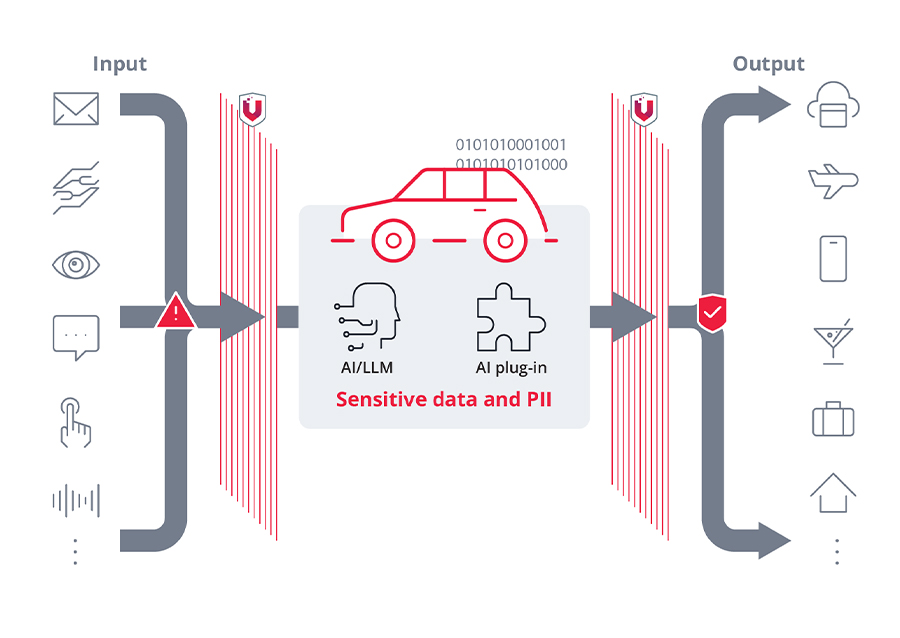
In-Vehicle AI Guardian
Our solutions shield your GenAI-based applications from data leaks caused by AI prompt injection, unsecure output, or vulnerable or unsecure third-party plug-ins — covering the OWASP top risks for LLM applications. We support your LLM, whether deployed in the cloud or at the edge.
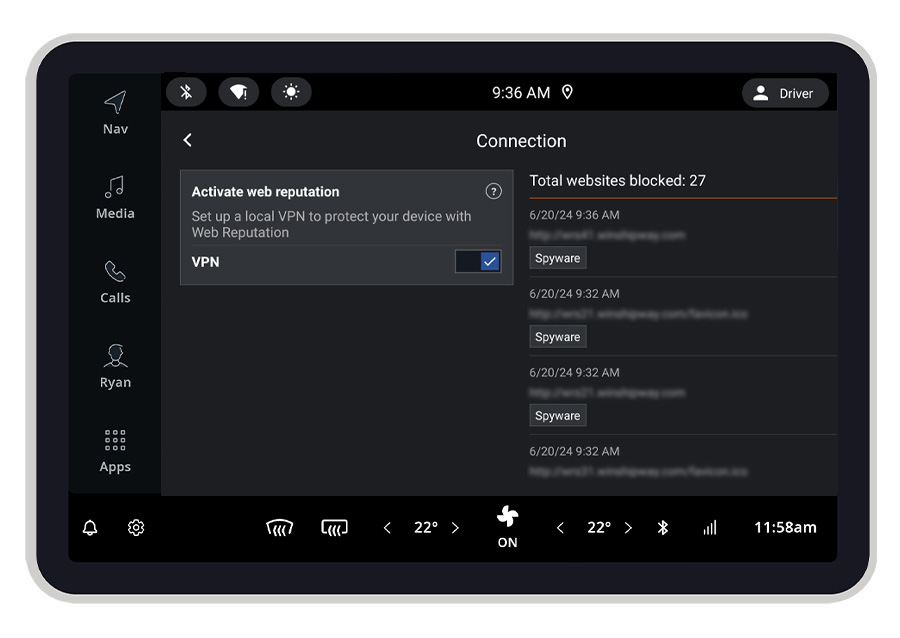
Browser Defense
Our solutions can detect vulnerable browsers and malicious URLs, promptly alerting car owners to suspicious website connections. This keeps users from inadvertently sharing sensitive data with phishing sites and effectively prevents remote attacks via browser vulnerabilities that could compromise in-vehicle infotainment (IVI) systems and affect vehicle safety.
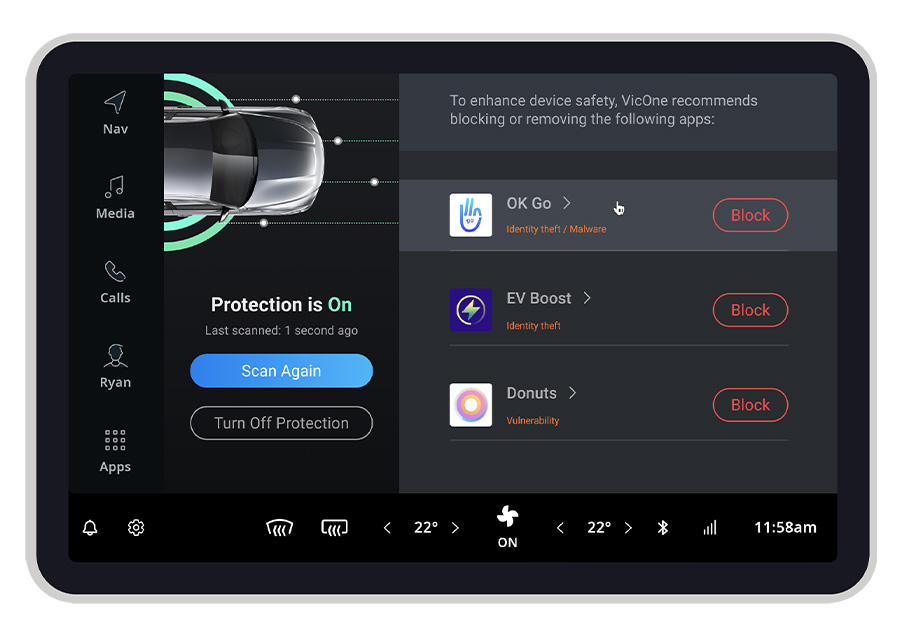
Risky App Detection
Our solutions detect risky apps that engage in suspicious API calls, access malicious URLs, or request sensitive or excessive permissions. This ensures robust protection of users' sensitive data and PII — from IVI systems to car companion mobile apps. Integrated with OEM or IVI supplier systems, our solutions empower car users to block risky apps. Utilizing a proven database with a 100% malicious app protection rate,* we deliver laser-sharp precision in detection.
*Source: AV-Comparatives Mobile Security Review 2022
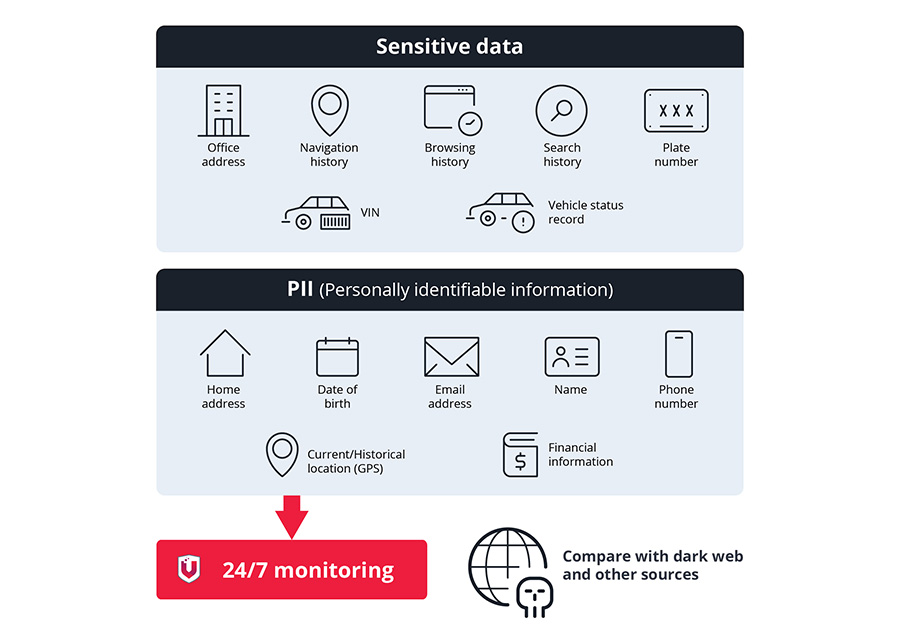
24/7 Data Monitoring
Our solutions vigilantly monitor the dark web and other parts of the internet for leaks of customers' PII and automotive-related sensitive data, such as VINs. Upon detecting a leakage, we immediately alert customers, empowering them to respond swiftly. Leveraging a proven monitoring service with over 12 billion leaked records found,* we provide the best coverage with earlier warnings in the market.
*Source: Trend Micro ID Security
Safeguarding Every Aspect of the Smart Cockpit
More Product Features
- Rogue and unsecure Wi-Fi detection: Our solutions detect unsafe Wi-Fi hotspots, identifying potential man-in-the-middle attacks and credential leakage risks. We promptly alert car users with a warning pop-up, ensuring that their security remains uncompromised. Read Recent Case
- One solution for all: We provide versatile deployment and integration options, including SDK and APK, to expedite time to market and streamline implementation.
- Enhanced risk visibility: Integrated with our xNexus next-gen VSOC platform, our solutions extend attack surface visibility from system to application level, empowering OEMs for unified cyber risk management.
- Marketplace app scanner: Our solutions scan for malware, viruses, APK weaknesses, APK vulnerabilities, and malicious AI plug-ins, ensuring that apps are safe before reaching app stores.
- Automotive mobile app protection: By integrating our SDK into automotive mobile apps, such as car companion apps or car insurance apps, OEMs and insurance companies can ensure that their apps run in a secure mobile environment, preventing leakage of personal data.
Our Collaborations
Know More From Our Resources
GAIN INSIGHTS INTO AUTOMOTIVE CYBERSECURITY
Prerequisites for Vulnerability Management in Automotive Cybersecurity in the AI Era
As AI accelerates exploit development, CVSS scores alone no longer suffice. Here's what automotive OEMs and suppliers must prioritize now.
READ MORE →Copy Fail and DirtyFrag: When Linux Kernel Flaws Become Automotive Cybersecurity Risks
Copy Fail (CVE-2026-31431) exposes how a Linux kernel flaw can impact automotive systems. See the risk, MITRE mapping, and xCarbon response.
READ MORE →VicOne Situational Awareness Report: Cybersecurity in the Automotive, Transportation, and Logistics Sectors in Q1 2026
VicOne recorded 405 automotive cybersecurity incidents in Q1 2026. Ransomware persisted, EV charging incidents tripled, and AI emerged as a new attack surface. This report breaks down the threats by region, domain, and vulnerability type.
READ MORE →AI Supply Chain Attacks Are Here: What Automotive OEMs Need to Know
AI supply chain attacks are no longer theoretical. VicOne's Automotive CyberThreat Research Lab breaks down how attackers are exploiting AI development tooling, why automotive OEMs face elevated exposure, and what security teams should do now.
READ MORE →